Details of awards received by the Signpost are here.



All contents copyright © 2005-19 Readout Publications
|
The Read-Out Instrumentation Signpost
Measurement, Control and Automation Resources throughout the World
Your advert here!
Last changes to this page: 9/8/2019
Cyber-Security
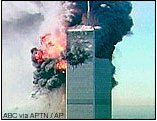
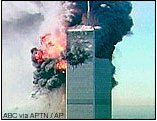 The events of September 11th 2001 focused our minds more than anything else on the vulnarability of our existance and the systems which govern everyday living and working.
The events of September 11th 2001 focused our minds more than anything else on the vulnarability of our existance and the systems which govern everyday living and working.
|
One of the most fundamental changes in process industry today is the introduction of electronic documentation. One of the areas that has received great attention is the integriy of the information and we have a page which deals with this aspect especially in regards to 21 CFR Part 11. However in the aftermath of the attack on the Twin Towers in New York more attention has been payed to the security aspect of business, especial the vital areas of the utilities, water, electricity and fuel. There is also an examination of other industries, food and pharmaceutical production and their vulnarability to cyber attack, whether planned or accidental as the downloading of some virus or worm.
"On January 25, 2003, the SQL Slammer Worm adversly affected the Bulk Electric System controls for at least two entities. I believe the consequences of the Slammer Worm incident in January 2003 effectively point to the potential risk to the electric industry of inadequate cyber security."
Chuck Noble, Information Security ISO New England
|
Without doubt the most serious event in cybersecurity was the discovery of Stuxnet malware in July 2010 . Here, Stuxnet & process cyber security threat links , we have listed links to many sites of interest in the understanding of this development with suggestions as to how to protect control systems from its effects. At first thought to be an ordinary bug which had located a gap in protection in industrial software it quickly was recognised to be a worm directed particularly at industrial control systems. Perhaps the most shocking thing about this is not that it occured but that the vendors (and the users) by and large appeared to be unprepared! , we have listed links to many sites of interest in the understanding of this development with suggestions as to how to protect control systems from its effects. At first thought to be an ordinary bug which had located a gap in protection in industrial software it quickly was recognised to be a worm directed particularly at industrial control systems. Perhaps the most shocking thing about this is not that it occured but that the vendors (and the users) by and large appeared to be unprepared!
|
Resources
ENISA The European Network and Information Security Agency, works for the European Union Institutions and Member States. ENISA is the EU's response to these cyber security issues of the European Union. As such, it is the 'pace-setter' for Information Security in Europe, and a centre of expertise.
The Repository of Industrial Security Incidents is a database of incidents of a cyber security nature that have (or could have) affected process control, industrial automation or Supervisory Control and Data Acquisition (SCADA) systems.
Security Pages from ISA "At any given time a company's security can be breached.
Companies must be proactive in making sure networks are safe
and must work daily to ensure threats are eliminated. With
security threats getting more sophisticated, so should your
company's security policy. Are you doing enough to protect
your company?"
ISA Courses on Cybersecurity
Black Hat Technical Security Conference - highly technical information security conferences that bring together thought leaders from all facets of the infosec world � from the corporate and government sectors to academic and even underground researchers ("good hackers").
The Federal Energy Regulatory Commission is an independent regulatory agency within the US Department of Energy. They have become innovative in the examination and insistance in standards for cyber security in the aftermath of the increased awareness of the vulnarability of important utilities, water, electricity etc to systematic or planned attack or indeed accidental damage through the abuse of the freedoms of internet.
The documment to look for is "Cyber Security Standards Docket RM01-12-000".
Cyber Security a useful gateway by at ARC.
Dow Cyber Security is a site which examines various standards.
Integrate Utility Electronic and Physical Security - A conference held in Chicago in June 2003.
The Federal Computer Incident Response Center (FedCIRC) is part of the US Department of Homeland Defence, the department set up after the New York massacre of September 11, 2001. Another section of this powerful department is the National Infrastructure Protection Centre.
The Cyber Security Policy & Research Institute (CSPRI) is a centre for GWU and the Washington (DC) area to promote the analysis of policy problems that have a significant computer systems component.
Establishment of a European Network and Information Security Agency - Like most things on EU websites this is difficult to navigate around but there is some useful information here.
|
Companies & Publications
Industrial Safety and Security Source (isssource) is a web-based information provider devoted solely to keeping manufacturers current on safety, cyber and physical security news, products, features, applications and trends. They publish The Shield each week.
Prosecuritytalk covers all aspects of the growing area of security. Edited by Jonathan Newell this will publish news in this field from Autumn 2005.
 Secure Systems Insider a web publication published by Control (Putnam Media Publication). Register for your copy here!
Secure Systems Insider a web publication published by Control (Putnam Media Publication). Register for your copy here!
While there are many companies which can provide "fire-wall" protection to date we have not come across many to provide a protection system in the control environment.
Armis "Armis discovers all devices in your environment, analyzes their behavior to identify risks or attacks, and protects your critical business information automatically."
Byres Security (Tofino) practical and effective industrial network security and SCADA* security products that are simple to implement and that do not require plant shutdowns. (Now part of Belden Group)
Industrial Defender (formerly Verano) with their Industrial Defender suite - introduced from June 2003.
Wurldtech - Protecting critical infrastructure from cyber-attacks. Company formed in 2006.
CISP Cyber Security - Cyber Security Compliance for Power, Oil & Gas, Water Treatment, NERC-CIP, NEI 0809 and CFATS. Doug Clifton, he Director of Critical Infrastructure and Security Practice (CISP) at Invensys Operations Management oversees this useful blog.
 Securing your PC - Is your PC the weak link in your company's system?
Securing your PC - Is your PC the weak link in your company's system?
Wolves at the Door(s) of the House of Straw (Dec'07) and Wolves at the Security House Door(s), Part 2 (Jan'08) are two relevent articles by Eric Byres in Control
Protecting against increasing external threats is an interesting set of pages and examples of actual events publishede by PA Consulting
Safety Considerations for SCADA/DCS Attacksby Jonathan Pollet Plant Data Technologies
Today's systems: Control, supervise, and secure!
by Brian Ahern Verano (now Industrial Defender)
Brian Ahern was one of the speakers at the 2003 Read-out Forum.
Intrusion detection and cybersecurity
Dale Peterson, who has been in the information business for twenty years, discusses this aspect. (May 2004).
One site with information on this topic and the Sarbanes-Oxley act is the Information
Systems Audit and Control Association
|
What is a Computer virus?
 A computer virus is a programme or software with a set of coded instructions to carry out the desired disorder and destruction, as also to replicate it. Though non-living and artificially created, the computer virus has marked similarities with its biological counterpart, and hence the name. Both forms of viruses contain coded instructions to carry out a set of activities, when certain specified conditions are met. Each computer virus has its specific signature. Both of them invade and replicate only in a host. Both of them can be detected and "vaccines" can be prepared. The creators of computer viruses are knowledgeable human beings, sadly displaying a sadistic desire to have fun at the cost of serious PC users at best or with serious political, vengeful or other malicious motivation. A computer virus is a programme or software with a set of coded instructions to carry out the desired disorder and destruction, as also to replicate it. Though non-living and artificially created, the computer virus has marked similarities with its biological counterpart, and hence the name. Both forms of viruses contain coded instructions to carry out a set of activities, when certain specified conditions are met. Each computer virus has its specific signature. Both of them invade and replicate only in a host. Both of them can be detected and "vaccines" can be prepared. The creators of computer viruses are knowledgeable human beings, sadly displaying a sadistic desire to have fun at the cost of serious PC users at best or with serious political, vengeful or other malicious motivation.
|
What is a worm?
 A program or algorithm that replicates itself over a computer network and usually performs malicious actions, such as using up the computer's resources and possibly shutting the system down. A program or algorithm that replicates itself over a computer network and usually performs malicious actions, such as using up the computer's resources and possibly shutting the system down.
|
|

Cyber Security in I&C
ISA Security Institute is a globally recognized body that is working toward establishing the ISASecure designation which identifies and promotes security compliant products and systems in the industrial automation industry.
Process Control Network Security Weak Links - How many of these are in your plant! (9/9/2009 - Process Automation Usability Project)
Chemical industry forging cyber-security plan - an article in ISA's INTECH website (24th June 2002).
ISA-SP99 ISA's Manufacturing and Control Systems Security Committee. (formed October 2002).
The State of Cyber Security in Automation on the Interkama site. (21st March 2003)
US Congress on SCADA Threat (Intech November 2003)

Could the next power cut be caused by computer sabotage? How safe is your system.
|

 , we have listed links to many sites of interest in the understanding of this development with suggestions as to how to protect control systems from its effects. At first thought to be an ordinary bug which had located a gap in protection in industrial software it quickly was recognised to be a worm directed particularly at industrial control systems. Perhaps the most shocking thing about this is not that it occured but that the vendors (and the users) by and large appeared to be unprepared!
, we have listed links to many sites of interest in the understanding of this development with suggestions as to how to protect control systems from its effects. At first thought to be an ordinary bug which had located a gap in protection in industrial software it quickly was recognised to be a worm directed particularly at industrial control systems. Perhaps the most shocking thing about this is not that it occured but that the vendors (and the users) by and large appeared to be unprepared!
 A computer virus is a programme or software with a set of coded instructions to carry out the desired disorder and destruction, as also to replicate it. Though non-living and artificially created, the computer virus has marked similarities with its biological counterpart, and hence the name. Both forms of viruses contain coded instructions to carry out a set of activities, when certain specified conditions are met. Each computer virus has its specific signature. Both of them invade and replicate only in a host. Both of them can be detected and "vaccines" can be prepared. The creators of computer viruses are knowledgeable human beings, sadly displaying a sadistic desire to have fun at the cost of serious PC users at best or with serious political, vengeful or other malicious motivation.
A computer virus is a programme or software with a set of coded instructions to carry out the desired disorder and destruction, as also to replicate it. Though non-living and artificially created, the computer virus has marked similarities with its biological counterpart, and hence the name. Both forms of viruses contain coded instructions to carry out a set of activities, when certain specified conditions are met. Each computer virus has its specific signature. Both of them invade and replicate only in a host. Both of them can be detected and "vaccines" can be prepared. The creators of computer viruses are knowledgeable human beings, sadly displaying a sadistic desire to have fun at the cost of serious PC users at best or with serious political, vengeful or other malicious motivation.
 A program or algorithm that replicates itself over a computer network and usually performs malicious actions, such as using up the computer's resources and possibly shutting the system down.
A program or algorithm that replicates itself over a computer network and usually performs malicious actions, such as using up the computer's resources and possibly shutting the system down.